Cybersecurity Risk Assessment—Probability and Impact Analysis 2025
Lab Title:
Cybersecurity Risk Assessment—Probability and Impact Analysis
Objective
To enable MSc-level students to:
- Understand and apply the concepts of probability and impact in risk analysis.
- Identify and assess cybersecurity risks within a simulated organizational context.
- Develop risk mitigation strategies based on analytical frameworks.
- Reflect on human factors and decision-making biases in risk perception.
Learning Outcomes of Cybersecurity Risk
By the end of the lab, students will be able to:
- Define key components of cybersecurity risk.
- Use a structured methodology to assess probability and impact of cybersecurity risks.
- Develop a prioritized risk register for a simulated organization.
- Formulate appropriate risk mitigation strategies.
- Critically evaluate the role of subjective and objective elements in risk assessment.
Lab Setup
- Time Required: 2–3 hours
- Software/Tools: Microsoft Excel / Google Sheets (for risk register), access to a simulated scenario, optional reference to risk assessment frameworks (e.g., NIST, ISO 27005)
- Lab Environment: Virtual lab, cybersecurity simulation platform or paper-based if tools unavailable
Lab Scenario: Simulated Organization
Scenario: You are part of the security team for ‘MedTech Solutions,’ a mid-sized healthcare technology provider. The company operates globally and manages sensitive patient health data. A recent internal audit identified several cybersecurity vulnerabilities.
Key Observations from the Audit:
- Unpatched critical vulnerabilities in public-facing web servers.
- Weak password policies for employee accounts.
- Legacy encryption algorithms in some database systems.
- Lack of regular data backups for critical systems.
- Multiple phishing emails reported by staff but no formal training program.
Are You Looking for Answer of This Assignment
Order Non Plagiarized Assignment
Cybersecurity Risk Lab Tasks
Task 1: Identify Key Risks
Step 1.1: Review the audit findings.
Step 1.2: Identify at least 5 distinct cybersecurity risks relevant to MedTech Solutions.
Step 1.3: Categorize the risks based on affected assets: Infrastructure, Devices, Users, Reputation.
Task 2: Assess Probability and Impact
Step 2.1: For each identified risk, estimate its probability (High, Medium, Low). Justify your reasoning.
Step 2.2: For each risk, estimate its potential impact (High, Medium, Low).
Step 2.3: Construct a Risk Register including: risk description, affected assets, probability, impact, risk priority score.
Task 3: Mitigation Strategy Development
Step 3.1: For the top 2 high-priority risks, develop detailed mitigation strategies.
Step 3.2: Include technical controls, policy changes, and user education measures.
Step 3.3: Estimate the feasibility and cost considerations for each mitigation.
Task 4: Critical Reflection
Step 4.1: Write a short reflection (~250 words) on how subjective judgment influences risk assessment.
Step 4.2: Discuss how organizational culture and decision-making processes affect risk prioritization.
Deliverables
- Risk Register: Completed Excel/Sheet document.
- Mitigation Strategy Report: ~500 words outlining strategies for the top 2 risks.
- Reflection Essay: ~250 words on subjective elements in risk assessment.
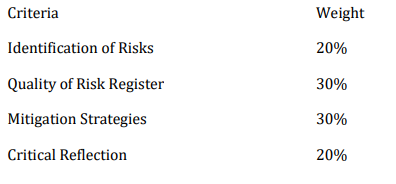
Assignment Criteria of Cybersecurity Risk
Extension / Advanced Task (Optional)
Research and apply a formal risk assessment framework (e.g., ISO 27005) to the scenario. Compare its structured output to your initial risk register